Introduction: The Encryption Race Against Quantum Computers
Imagine a computer powerful enough to break today’s encryption in minutes.
That is not science fiction anymore.
Quantum computing is advancing rapidly, and experts believe that future quantum machines could crack many current encryption systems that protect our banking, emails, and online identities.
This threat has pushed researchers and governments worldwide to develop quantum-resistant encryption algorithms.
One of the most promising solutions is CRYSTALS-Kyber encryption, a cutting-edge cryptographic system designed to protect data even against quantum attacks.
In fact, it has already been selected by the U.S. National Institute of Standards and Technology (NIST) as a new global standard for post-quantum cryptography.
This guide explains everything about crystal kyber encryption, including:
- how it works
- why it is important
- real-world applications
- future developments
By the end of this article, you will understand why Kyber encryption may soon protect most of the world’s digital communication.
What Is Crystal Kyber Encryption?
Crystal Kyber encryption, formally called CRYSTALS-Kyber, is a post-quantum cryptographic algorithm designed to secure data against attacks from quantum computers.
It belongs to a category called:
Lattice-Based Cryptography
Instead of relying on traditional mathematical problems like factoring large numbers, Kyber uses complex lattice mathematics, which is believed to be resistant to quantum attacks.
Quick Definition
Crystal Kyber encryption is a quantum-resistant key encapsulation mechanism (KEM) that enables secure key exchange between two parties.
This makes it ideal for:
- secure internet communication
- encrypted messaging
- VPNs
- cloud security
Quick Summary Table
| Feature | Description |
|---|---|
| Algorithm Name | CRYSTALS-Kyber |
| Type | Post-Quantum Cryptography |
| Mathematical Basis | Lattice-Based Cryptography |
| Standardized By | NIST |
| Purpose | Secure key exchange |
| Security Level | Quantum-Resistant |
Why Crystal Kyber Encryption Is Important Today
Cybersecurity is facing a major challenge.
Current encryption algorithms such as RSA and ECC could eventually be broken by large-scale quantum computers.
This creates a major risk for:
- banking systems
- government communication
- national security
- cloud storage
- internet infrastructure
Kyber encryption solves this problem by using quantum-resistant mathematics.
Key Reasons Kyber Matters
1. Protection Against Quantum Attacks
Kyber is designed to remain secure even if powerful quantum computers exist.
2. Faster Than Other Post-Quantum Algorithms
Compared to many alternatives, Kyber offers:
- fast encryption
- efficient performance
- smaller keys
3. Global Standardization
In 2022, the NIST Post-Quantum Cryptography Project selected Kyber as the primary algorithm for secure key exchange.
External resource:
https://www.nist.gov/news-events/news/2022/07/nist-announces-first-four-quantum-resistant-cryptographic-algorithms
4. Future Internet Security
Kyber may soon protect:
- HTTPS websites
- VPN connections
- messaging platforms
- IoT networks
Historical Background: The Rise of Post-Quantum Cryptography
To understand Kyber, we must understand the evolution of encryption.
Traditional Encryption Era
For decades, the internet relied on algorithms like:
| Algorithm | Introduced |
|---|---|
| RSA | 1977 |
| Diffie-Hellman | 1976 |
| Elliptic Curve Cryptography | 1985 |
These algorithms rely on mathematical problems that classical computers cannot solve easily.
Quantum Threat
Quantum computers can run Shor’s Algorithm, which can break these systems much faster.
Researchers realized that the internet needed new encryption technologies.
The NIST Competition
In 2016, NIST launched a global competition to develop quantum-safe cryptography.
After years of evaluation, several algorithms were selected.
Kyber emerged as the leading candidate for secure key exchange.
Official information:
https://csrc.nist.gov/projects/post-quantum-cryptography
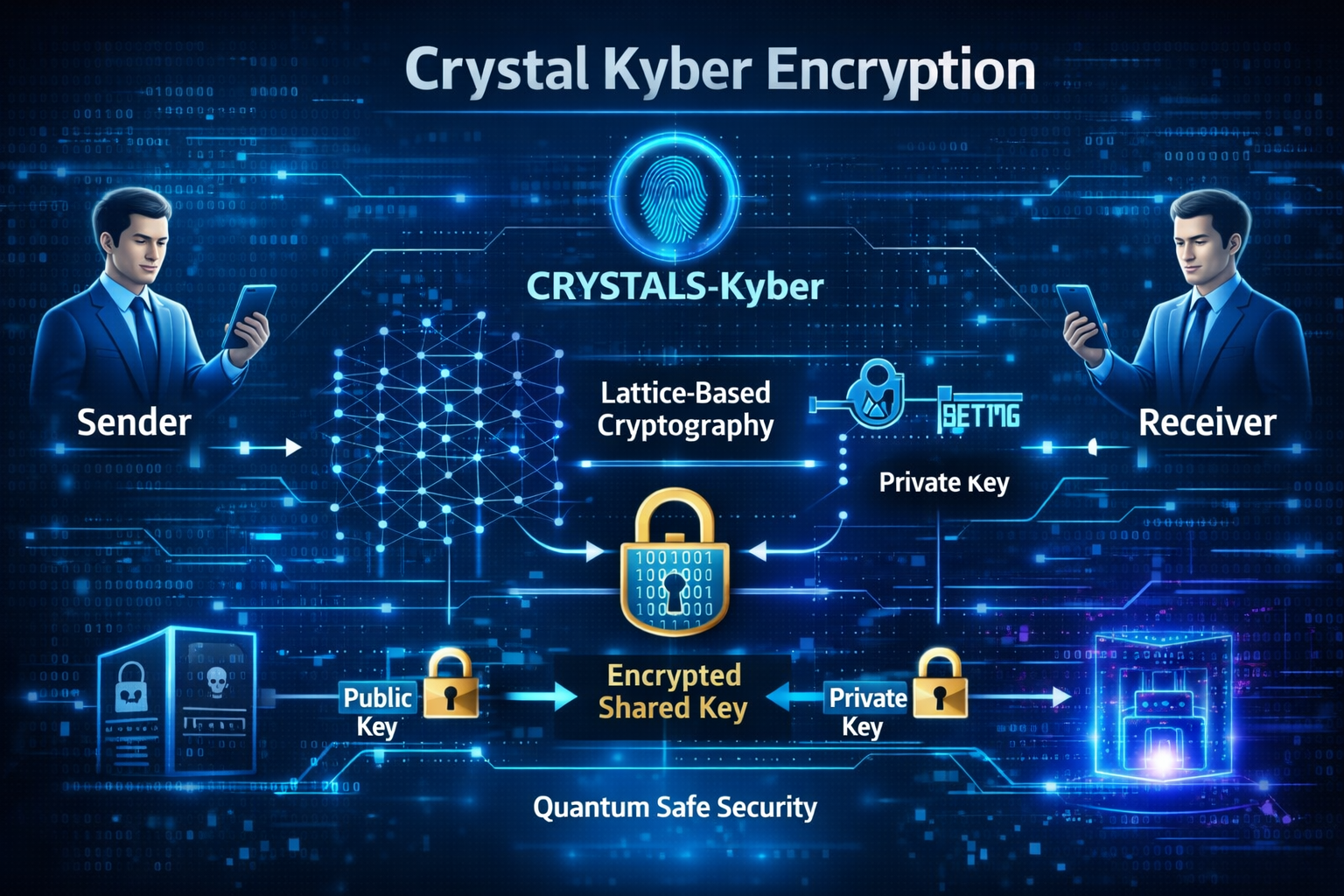
How Crystal Kyber Encryption Works
Kyber uses advanced mathematics called Module-Lattice problems.
These problems are extremely difficult to solve, even for quantum computers.
Simplified Step-by-Step Process
Step 1: Key Generation
The system generates:
- a public key
- a private key
The public key can be shared openly.
Step 2: Encryption
The sender uses the receiver’s public key to encrypt a secret value.
Step 3: Encapsulation
Kyber creates a shared secret called a session key.
Step 4: Decryption
The receiver uses their private key to recover the shared secret.
Step 5: Secure Communication
Both parties now use the shared key to encrypt further communication.
Simplified Flow Diagram
Sender → Public Key → Kyber Algorithm → Encrypted Secret → Receiver → Private Key → Shared Key
Real-World Applications of Kyber Encryption
Kyber is already being integrated into modern security systems.
1. Internet Security (HTTPS)
Future web browsers may use Kyber to secure HTTPS connections.
2. Secure Messaging
Messaging apps may adopt Kyber for quantum-safe communication.
3. Cloud Security
Cloud providers are exploring Kyber encryption to protect stored data.
4. Government Communication
Government agencies are already testing post-quantum encryption systems.
5. VPN Security
Next-generation VPNs will likely use Kyber-based key exchange protocols.
Did You Know?
Some encrypted data stolen today could be stored by hackers and decrypted later when quantum computers become powerful enough.
This strategy is called:
Harvest Now, Decrypt Later
Post-quantum encryption like Kyber prevents this risk.
Benefits of Crystal Kyber Encryption
Kyber offers several advantages compared to traditional encryption systems.
Major Advantages
| Benefit | Explanation |
|---|---|
| Quantum Resistance | Secure against future quantum computers |
| High Speed | Faster than many PQC algorithms |
| Efficient Keys | Smaller key sizes |
| Scalable | Works for large systems |
| Standardized | Approved by NIST |
Challenges and Risks
Despite its promise, Kyber encryption still faces challenges.
1. Implementation Complexity
Integrating Kyber into existing systems requires careful engineering.
2. Compatibility Issues
Older systems may not support post-quantum algorithms.
3. New Attack Research
Although Kyber is considered secure, cryptographers continue studying potential vulnerabilities.
Future Trends in Post-Quantum Encryption
Kyber is only the beginning.
Several new cryptographic technologies are emerging.
1. Hybrid Encryption Systems
Future systems may combine:
- classical encryption
- post-quantum encryption
2. Quantum-Safe Internet
Major technology companies are preparing for quantum-secure protocols.
3. Hardware Security Integration
Post-quantum encryption may be built directly into processors.
4. Global Cybersecurity Standards
Countries are developing quantum-safe security policies.
Research reference:
https://www.ncsc.gov.uk/information/post-quantum-cryptography
Expert Tip
Cybersecurity experts recommend preparing for post-quantum migration early.
Organizations should:
- audit existing encryption systems
- monitor post-quantum standards
- plan gradual algorithm upgrades
Practical Tips for Readers
If you work in cybersecurity or IT, start preparing now.
Preparation Steps
- Learn post-quantum cryptography basics
- Monitor NIST updates
- Evaluate cryptographic libraries
- Implement hybrid encryption
- Upgrade security infrastructure gradually
Related Cybersecurity Resource
For broader encryption concepts, read:
Encryption Techniques Explained
https://blog.aquartia.in/encryption-techniques-guide
Another helpful guide:
Understanding Mobile Privacy and Security
https://blog.aquartia.in/mobile-privacy-security
Summary
Crystal Kyber encryption represents one of the most important breakthroughs in modern cybersecurity.
As quantum computing advances, traditional encryption systems may become vulnerable.
Kyber offers a future-proof cryptographic solution designed to protect global digital infrastructure.
From secure internet communication to government systems, Kyber may soon become the foundation of next-generation encryption standards.
4. FAQ SECTION
What is CRYSTALS-Kyber encryption?
CRYSTALS-Kyber is a post-quantum cryptographic algorithm designed to protect digital communication against attacks from quantum computers. It uses lattice-based mathematics instead of traditional factorization problems used by RSA or ECC. Kyber is primarily used for secure key exchange and has been selected by the National Institute of Standards and Technology (NIST) as a standard for post-quantum encryption. This makes it one of the most promising solutions for protecting internet communication, financial systems, and sensitive data in the quantum computing era.
Why is Kyber encryption considered quantum-safe?
Kyber encryption relies on lattice-based mathematical problems that are extremely difficult for both classical and quantum computers to solve. Unlike RSA or elliptic curve cryptography, which can be broken by Shor’s algorithm on a quantum computer, lattice-based cryptography does not currently have an efficient quantum attack method. Because of this, Kyber is considered resistant to future quantum threats and suitable for long-term security systems.
Who developed CRYSTALS-Kyber?
CRYSTALS-Kyber was developed by a team of cryptography researchers from leading institutions including KU Leuven, Radboud University, and IBM Research. It was submitted to the NIST Post-Quantum Cryptography competition, where it underwent several years of security evaluation. After extensive testing and peer review, Kyber was selected by NIST as one of the first algorithms to become a global post-quantum encryption standard.
How is Kyber different from RSA encryption?
RSA encryption relies on the difficulty of factoring large numbers, which quantum computers could potentially solve quickly. Kyber, on the other hand, uses lattice-based mathematical problems that remain difficult even for quantum computers. Kyber also provides faster performance and smaller key sizes compared to many other post-quantum algorithms, making it practical for real-world internet applications.
Where will Kyber encryption be used?
Kyber encryption will likely be used in many digital systems including secure internet connections (HTTPS), VPN networks, encrypted messaging platforms, cloud computing environments, and government communication networks. Technology companies and cybersecurity organizations are already testing Kyber-based implementations to prepare for future quantum-safe security systems.
What is lattice-based cryptography?
Lattice-based cryptography is a cryptographic technique that uses complex mathematical structures called lattices. These lattices represent multidimensional grids of points. Certain computational problems related to lattices are extremely difficult to solve efficiently, making them ideal for building secure encryption systems. Kyber encryption relies on these hard lattice problems to create secure key exchange mechanisms.
When will post-quantum encryption become standard?
Many cybersecurity experts believe post-quantum cryptography will start becoming widely deployed between 2025 and 2030. Governments and technology companies are already testing quantum-safe encryption systems to replace traditional algorithms like RSA. The standardization of Kyber by NIST is a major step toward this transition.
Can quantum computers break Kyber encryption?
Currently, there are no known practical quantum attacks capable of breaking Kyber encryption. While researchers continue studying potential weaknesses, Kyber is considered one of the most secure algorithms for protecting data against future quantum computing threats. Continuous research and security analysis will ensure its long-term reliability.
5. KEY TAKEAWAYS
📦 Important Insights
- Crystal Kyber encryption is a post-quantum cryptographic algorithm
- It protects data from future quantum computer attacks
- Selected by NIST as a global encryption standard
- Based on lattice-based cryptography
- Expected to secure the future internet
6. CONCLUSION
Quantum computing is set to transform technology—and cybersecurity must evolve alongside it.
Crystal Kyber encryption represents one of the most promising solutions for protecting digital communication in the quantum era.
By adopting post-quantum encryption today, organizations and governments can ensure that sensitive information remains secure for decades to come.
The transition to quantum-safe cryptography has already begun, and Kyber is likely to play a central role in the future of internet security.





+ There are no comments
Add yours