Key Highlights
- Cybersecurity powers business growth, not just defense or compliance.
- Embedding security in design and operations creates competitive differentiation.
- Identity-based protection, automation, and managed services strengthen resilience.
- Proactive threat intelligence fuels innovation and customer trust.
- Shifting the mindset from reactive to strategic security delivers lasting business value.
Cybersecurity is evolving fast—and for modern businesses, it’s no longer just a locked door against digital threats. Instead, leading companies are embedding security into the heart of their products, infrastructure, and daily operations, unlocking new avenues for growth, innovation, and customer loyalty.
From identity-based protection and automated threat responses to proactive intelligence and managed services, organizations are transforming cybersecurity from a passive precaution into a powerful differentiator. In this blog, we explore how security-driven strategies position you for resilience, trust, and long-term success—and why waiting for the next breach isn’t an option.
From Afterthought to Core Strategy: Security’s New Business Role

Historically, cybersecurity was a ‘back-office’ function—activated only after breaches or compliance audits. But with digital transformation, cloud adoption, and rising cybercrime, top organizations now treat security as a core business enabler.
What does this shift look like?
- Product design with security in mind: Build secure apps from day one, so customers trust and adopt your products faster.
- Secure infrastructure: Bake protections into cloud, network, and workplace systems, supporting safe innovation.
- Security across operations: Automate access controls and data monitoring to enforce defense everywhere, not just at the perimeter.
- Continuous engagement: Security teams work alongside product and sales, ensuring risks are identified—and neutralized—before launch.
Identity-Based Protection: The Foundation of Resilient Security
One major transformation is the move towards identity-based security. Rather than simply blocking threats at the network edge, businesses now focus on:
- Strong authentication (multi-factor, biometrics) for users and devices.
- Smart access controls, granting only necessary permissions for each individual, app, or system.
- Real-time monitoring to spot suspicious logins or behavior and stop breaches before damage occurs.
Benefits:
This approach prevents identity theft, data leaks, and insider risks—while also making onboarding, collaboration, and customer experiences frictionless.
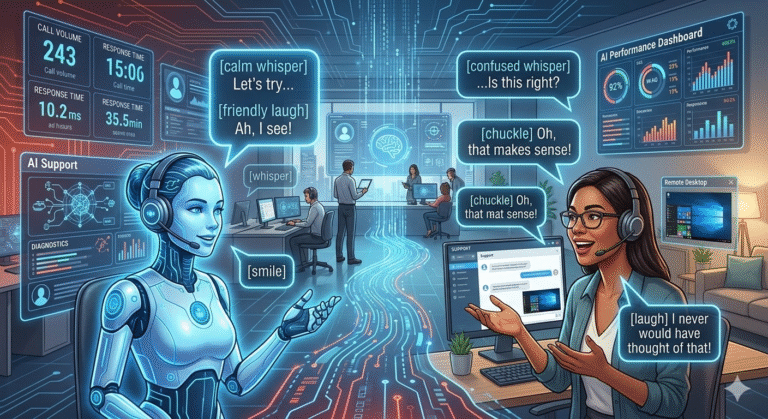
Automation and Managed Services: Safety at Scale
Cybersecurity today is a symphony of automated, adaptive systems. Advanced companies use:
- Automated threat detection: AI-driven platforms continuously scan for vulnerabilities and block threats in milliseconds.
- Response automation: Systems can quarantine devices, shut down malicious activity, and alert stakeholders without manual approval.
- Managed security services: Outsourcing certain security operations (SOC, endpoint detection, compliance) to specialists allows companies to focus on innovation rather than firefighting.
Result:
Business moves faster, protected by responsive layers of defense that adapt to both known and unknown threats.
Proactive Threat Intelligence: Turning Risks Into Opportunities
Rather than reacting to attacks, proactive organizations leverage threat intelligence:
- Monitor global threat feeds for the latest cyber tactics, malware, and fraud trends.
- Analyze emerging risks and simulate attacks to identify weak spots before adversaries do.
- Use insights to guide product development, security investments, and customer outreach.
Why it matters:
Customers want assurance their partners understand—and stay ahead of—cyber risks. Companies that demonstrate vigilance position themselves as trusted leaders.
Security as a Differentiator: Driving Innovation and Customer Trust
When security is embedded from the start:
- Customers notice, choosing partners that protect their data and privacy.
- Regulators give preference to platforms with strong compliance and governance.
- Investors see resilience, lowering risk and boosting confidence.
- Employees and users feel empowered, not burdened by clumsy controls.
Bottom line:
Security done right fuels innovation. Teams can launch products, test new ideas, and win contracts—knowing risks are managed and trust is built-in.
From Passive Defense to Business Accelerator: Action Steps
Ready to make cybersecurity a growth engine? Here’s how:
- Audit Your Current Security Culture
- Is security reactive or proactive? Integrated or siloed?
- Build Security by Design
- Collaborate between IT, product, legal, and business teams from the start of every project.
- Invest in Identity and Automation
- Enable multi-factor authentication, privileged access management, and AI-driven threat monitoring.
- Choose the Right Partners
- Managed services and security experts bridge gaps and bring best practices to your operations.
- Communicate Value
- Highlight your security investments in marketing, customer communications, and investor outreach.
Embracing Cybersecurity for Sustainable Success
For modern businesses, the real risk isn’t being attacked—it’s failing to innovate or inspire trust because cybersecurity is an afterthought. By transforming cybersecurity into a foundational driver, companies secure not just their data, but their growth, reputation, and future.




+ There are no comments
Add yours