KEY TAKEAWAYS
- Data is the New Currency of War: Information collection, algorithmic processing, and cybersecurity protection are now just as critical as physical weaponry in determining military success.
- Speed is Absolute Survival: AI-driven Super-OODA loops allow militaries to accurately predict and react to enemy movements in milliseconds, far surpassing human cognitive limits.
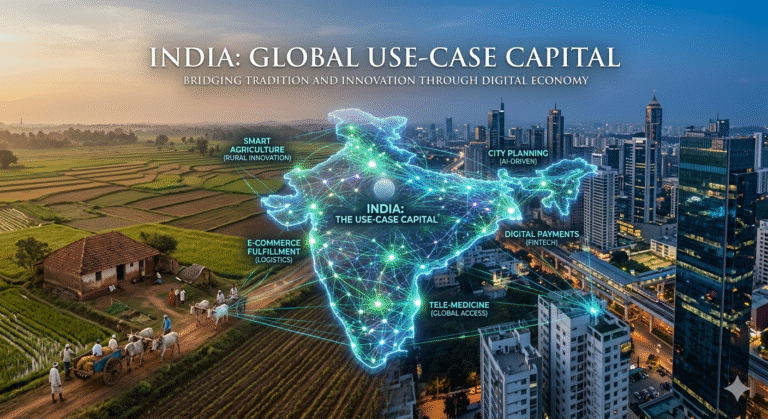
- Sovereignty Requires Indigenization: Projects like India’s Ekam highlight the absolute necessity for nations to build secure, domestic AI platforms to prevent foreign espionage and tech dependency.
- Commercial Tech is Embedded: Private companies are increasingly entrenched in military command structures, providing crucial cloud computing, predictive AI targeting, and satellite infrastructure.
- Ethics Lag Behind Technology: The rapid deployment of autonomous weapons vastly outpaces the development of international humanitarian law, creating severe accountability challenges on the battlefield.
The battlefields of the 21st century no longer rely solely on the physical massing of troops or the sheer volume of artillery fire. The vanguard of global conflict has migrated to an invisible, omnipresent domain: the digital data fabric.
In modern combat, the speed at which a military force aggregates, analyzes, and acts upon digital information determines the victor long before the first kinetic shot is fired. We have entered the era of data-driven warfare.
This transformation represents a complete doctrinal evolution in global security. It integrates artificial intelligence (AI), machine learning, autonomous drone swarms, and edge computing into the very marrow of military command.
From Ukraine’s algorithmic targeting systems to India’s secure smart combat ecosystem, data is no longer just a passive enabler of combat. It is an active weapon, a primary strategic asset, and a fiercely contested military objective.
Why This Topic Matters Today
The urgency of understanding algorithmic warfare has never been greater. Geopolitical power is actively shifting from nations with the largest standing armies to those with the most sophisticated computational capabilities.
Conflicts currently unfolding across the globe act as live laboratories for these emerging technologies. The war in Ukraine and the escalating strategic operations in West Asia demonstrate how data directly dictates survival and dominance .
Simultaneously, the integration of private technology companies into sovereign military operations is rapidly eroding traditional state-centric models of warfare. Militaries now rely heavily on commercial infrastructure for survival.
For defense professionals, policymakers, and civil services aspirants analyzing global security paradigms, understanding this shift is mandatory. The traditional “fog of war” is actively being replaced by the hyper-visible “military cloud”.
Key Highlights
| Strategic Component | Core Implication |
| The Super-OODA Loop | AI compresses traditional decision-making cycles into near-instantaneous machine-to-machine responses. |
| Data as a Strategic Asset | Information now ranks alongside military hardware and natural resources as a foundational pillar of national security. |
| Decentralized Execution | Modern networks push tactical decision-making to the edge while heavily centralizing reliance on commercial tech. |
| Accountability Black Holes | AI targeting systems raise unprecedented ethical questions regarding automation bias and international law. |
| Technological Indigenization | Nations are racing to build sovereign digital platforms to prevent foreign espionage and tech dependency. |
Background / Context
Historically, military dominance was achieved through kinetic superiority. The side capable of inflicting the most physical destruction generally secured the victory.
This paradigm began to shift during the Cold War with the conceptualization of the OODA loop by US Air Force Colonel John Boyd. The theory posited that the military force capable of cycling through Observation, Orientation, Decision, and Action faster than its opponent would inevitably win.
However, human cognition has a strict sequential limit. Traditional OODA loops are linear and fundamentally constrained by the speed of human thought and communication.
Modern conflict has evolved into Joint All-Domain Command and Control (JADC2). This concept demands simultaneous, highly coordinated operations across land, sea, air, space, and cyberspace.
To manage this overwhelming complexity, militaries are replacing human sequential processing with AI-driven predictive analytics. This technological leap transforms the traditional OODA loop into a highly adaptive “Super-OODA” cycle.
Core Explanation
Understanding the mechanics of data-driven warfare requires analyzing its fundamental components, operational mechanisms, and the primary stakeholders involved.
What It Is
Data-driven warfare is the continuous gathering, fusion, and exploitation of vast datasets to establish a decisive information edge. It relies heavily on cognitive defense systems that blend human command with machine cognition.
This approach utilizes satellite imagery, radar telemetry, acoustic signals, and open-source social media data. By processing these massive inputs, militaries achieve situational awareness at a scale and speed previously considered unimaginable.
How It Works: Compressing the Kill Chain
The fundamental goal of this digital architecture is to compress the “kill chain”—the time elapsed between detecting a target and neutralizing it.
First, networks of drones, satellites, and ground troops act as distributed sensors, generating terabytes of raw data. Next, AI algorithms ingest this data, filter out irrelevant noise, identify patterns, and highlight high-value targets.
Finally, machine-to-machine interfaces automatically relay these precise target coordinates to precision-guided munitions or autonomous drone swarms for immediate execution.
Key Components and Stakeholders
The modern battlespace involves a highly complex, interconnected web of actors. Sovereign militaries drive the demand for interoperability, seeking strategic advantages over their adversaries.
Defense technology firms and agile startups supply the algorithmic engines, computer vision platforms, and essential cloud infrastructure.
Crucially, civilian populations often unknowingly contribute to this ecosystem. Through smartphones, open-source intelligence (OSINT), and social media activity, they create a new environment of “participatory warfare”.
Expert Tip: When evaluating a modern military’s readiness, raw troop numbers are increasingly secondary. The true metric of modern combat readiness is the seamless interoperability of a nation’s data fabric across all its service branches.
Technical / Conceptual Breakdown
The transition to algorithmic warfare is supported by several highly advanced technological pillars. These systems operate continuously in the background to maintain military superiority.
- AI Battlefield Analytics: These are real-time data pipelines that feed satellite, reconnaissance, and radar inputs directly into AI decision models. These systems utilize predictive modeling to accurately forecast enemy logistics and unit behavior.
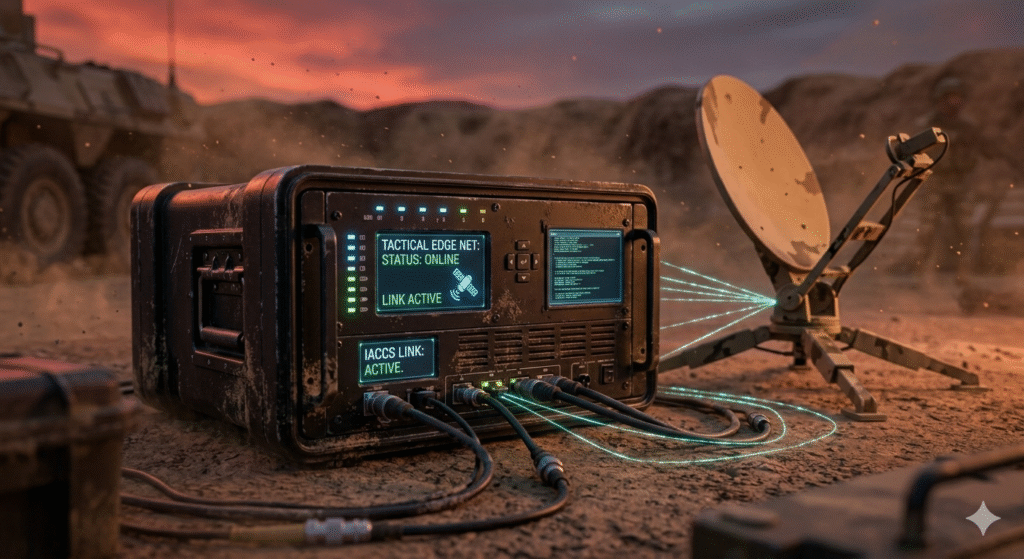
- Tactical Edge Computing: Centralized data centers often suffer from severe latency and are vulnerable to severed communication lines. To counter this, militaries push computing power to the “edge”—installing processing units directly onto drones, vehicles, and soldier wearables.
- AI-as-a-Service (AIaaS): Militaries are increasingly adopting AIaaS models. By utilizing pre-trained models and inference endpoints hosted on managed platforms, armed forces can accelerate the deployment of sophisticated tools without requiring ground-up development.
- Multisensor Fusion: This involves the seamless integration of disparate data streams. Thermal imaging, acoustic signatures, and electronic intelligence are merged into a single, cohesive Common Operating Picture (COP) for commanders.
Real-World Examples / Case Studies
To truly grasp the magnitude of this shift, we must examine the live deployment of these systems across different geopolitical theatres.
1. Ukraine: The Delta System and Commercial Integration
The conflict in Ukraine serves as the definitive genesis of modern participatory warfare. At the absolute heart of Ukraine’s defense is the Delta System, a highly advanced digital battle management platform .
Delta aggregates data from radar, human observers, and live drone feeds into a unified interface. Utilizing robust AI platforms, Delta routinely identifies thousands of pieces of enemy equipment weekly, dramatically compressing the kill chain and saving lives.
Crucially, Ukraine’s defense highlights a profound reliance on commercial technology. Private companies process immense volumes of civilian and military data to provide predictive targeting. While Western software often requires robust internet connections, systems like Delta are specifically designed to function offline at the tactical edge.
2. The United States: JADC2 and Project Maven
The US Department of Defense is spearheading the Combined Joint All-Domain Command and Control (CJADC2) initiative. This massive structural overhaul aims to connect sensors from all military branches into one unified data fabric.
A foundational element of this strategy is Project Maven. This ambitious AI and computer vision program automates the detection and classification of objects from drone surveillance videos, generating actionable intelligence at staggering speeds.
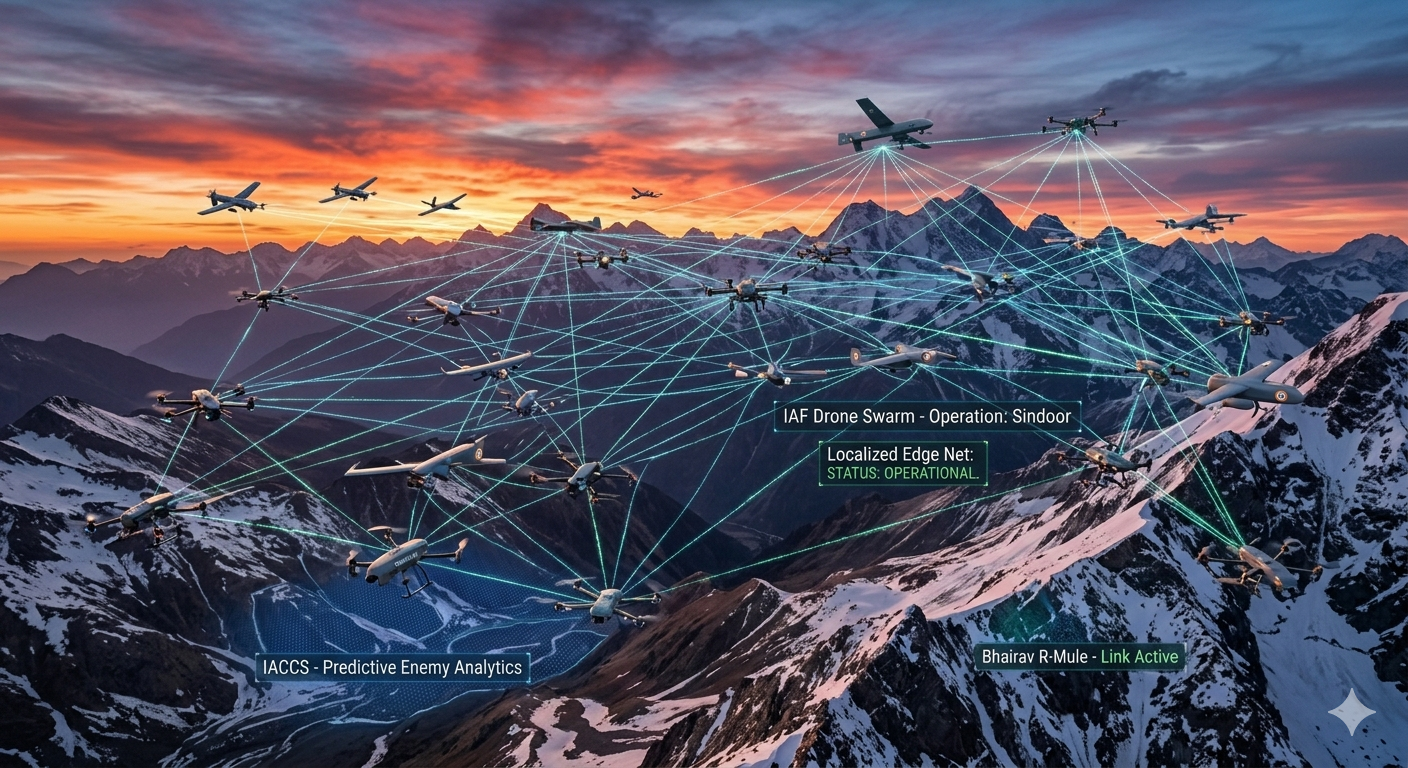
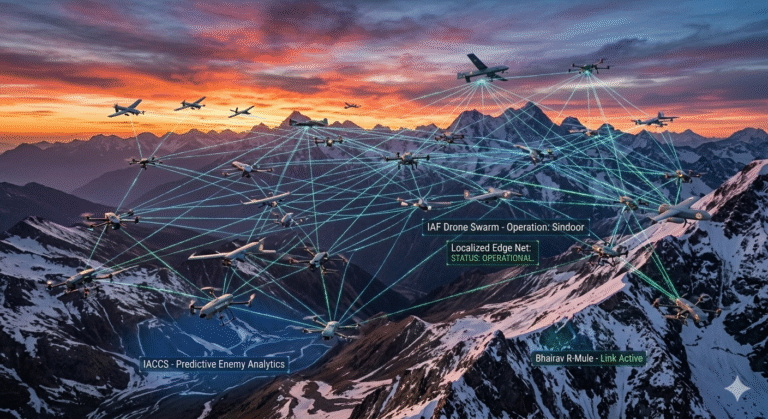
3. India: Project Ekam and Cognitive Defense
India is rapidly overhauling its defense ecosystem to counter evolving border threats, placing a massive emphasis on building a smart combat ecosystem.
Under the umbrella of the Atmanirbhar Bharat (self-reliant India) initiative, the Indian Army launched Project Ekam. This is a fully indigenous and secure AI platform designed explicitly for classified environments.
Project Ekam ensures digital sovereignty by completely removing dependence on foreign cloud providers. This allows personnel to analyze intelligence and manage documents securely. It is complemented by specialized tools like Trinetra for unified intelligence, XFace for facial recognition, and the integration of highly offensive drone swarms.
4. 2026 US-Iran War: Operation Epic Fury
Highlighting a near-future scenario, the 2026 conflict designated as Operation Epic Fury underscores the devastating efficiency of data-centric warfare.
Driven by overwhelming aerial coordination, the campaign utilized immense data streams to accurately eliminate 90% of targeted ballistic missile and drone capabilities within the first phase. The transition from expensive standoff cruise missiles to precision-guided Joint Direct Attack Munitions (JDAMs) reflected a high-confidence, data-rich operational environment. For more context on the geopolitical fallout of this scenario, explore our deep dive into the 2026 Fuel Crisis.
Benefits / Advantages
The integration of data and AI into warfare yields profound asymmetric advantages that fundamentally alter battlefield calculus.
By processing thousands of combat variables instantly, AI grants commanders absolute decision dominance. This pivotal shift from human sequential thinking to machine-enabled “Matrix Operations” allows for simultaneous, multi-vector combat strategies that overwhelm traditional defenses .
Furthermore, automated target recognition conserves vital intelligence, surveillance, and reconnaissance (ISR) resources for situations where they are most critically needed.
Drone swarms and unmanned ground systems actively remove human soldiers from the most hazardous frontline roles while flawlessly executing complex maneuvers. Simultaneously, indigenous platforms like India’s Project Ekam protect national data sovereignty, ensuring military intelligence remains secure from foreign corporate backdoors.
Challenges / Risks / Criticism
Despite the immense tactical allure, algorithmic warfare introduces unprecedented technical, ethical, and legal vulnerabilities that militaries are struggling to solve.
The Energy and Thermal Crisis at the Tactical Edge
Artificial Intelligence is exceptionally resource-intensive. Modern military data centers require tens of megawatts of power to function.
Training large-scale AI models consumes massive amounts of electricity, creating a vast energy footprint. At the tactical edge, high-performance computing faces severe Size, Weight, and Power (SWaP) constraints.
Advanced processors, such as the NVIDIA Blackwell B200, consume up to 1,200 watts per chip. Dissipating this extreme heat and securing reliable energy sources in rugged, hostile environments remains a critical, unsolved logistical bottleneck for field commanders.
The Accountability Black Hole
Ethicists consistently warn of an “accountability black hole” created by the deployment of autonomous lethal systems.
When an AI system misidentifies a civilian convoy as a military target due to algorithmic bias or a sensor failure, legal responsibility fractures completely. Programmers cannot possibly anticipate all battlefield variables in a lab.
Commanders disclaim direct responsibility for machine autonomy, and manufacturers cite technical complexity to evade strict liability. This tripartite vacuum makes war crimes procedurally unavoidable yet legally unpunishable.
Algorithmic Bias and Dehumanization
Machine learning models are strictly as objective as their underlying training data.
If an AI is trained predominantly on datasets characterizing “enemy behavior” as groups of young men carrying objects, it may erroneously target civilians carrying agricultural tools.
Furthermore, using AI to calculate acceptable casualty attrition rates fundamentally dehumanizes conflict. It reduces human lives—both soldier and civilian—to mere disposable data points in a cold, algorithmic cost-benefit equation.
Is Data a Legal Military Target?
As data becomes fundamental to military operations, international law desperately struggles to categorize it.
According to the Tallinn Manual 2.0, authored by international legal experts, data is inherently intangible. Therefore, it does not legally qualify as a traditional “object” under the established Law of Armed Conflict.
Consequently, deleting or heavily corrupting military data might not technically constitute an “attack” under current legal frameworks. This creates a highly perilous gray zone for cyber warfare and the attribution of state responsibility .
Global Implications
The rapid rise of the smart combat ecosystem forces a dangerous renegotiation of sovereign power. Militaries worldwide are becoming precariously dependent on private technology firms.
Companies that provide vital cloud infrastructure, satellite communications, and AI analytics are effectively embedded in the core decision-making architecture of modern warfare. Because these firms are commercially driven and legally beholden to shareholders, their operational incentives may eventually diverge from the national security imperatives of the states they serve.
Policymakers must actively regulate this “new war ecology.” They must ensure that sovereign states maintain ultimate control over their command-and-control infrastructures, rather than fully outsourcing them to Silicon Valley.
Furthermore, the ongoing militarization of space is intrinsically linked to data warfare. Satellites provide the indispensable backbone for intelligence gathering, missile early-warning systems, and secure communications. Recognizing this absolute reliance, NATO recently classified space as a formal operational domain, instantly triggering a global race to develop anti-satellite weapons.
Future Trends / Outlook
The immediate trajectory of military technology points toward a much deeper integration of unbridled autonomy and artificial intelligence.
Future combat will move rapidly beyond the sequential OODA loop. “Matrix Thinking” will allow AI systems to execute simultaneous, non-linear operations across multiple domains instantly.
Cognitive Electronic Warfare will also become standard. AI will autonomously detect and immediately adapt to enemy radar and communication jamming in real-time, rewriting electronic warfare signatures on the fly without human input.
Despite this, militaries will strive for Hybrid Human-Machine Teaming. While machines will handle the heavy data processing and tactical execution, the ultimate authority regarding the use of lethal force will ideally remain human. Ethical frameworks, such as India’s Evaluating Trustworthy Artificial Intelligence (ETAI), are currently being developed to ensure AI reliability.
Comparison Table: Kinetic Warfare vs. Data-Centric Warfare
The following table synthesizes the fundamental paradigm shift from traditional kinetic conflict to modern data-driven hybrid warfare.
| Feature | Traditional Kinetic Warfare | Data-Centric / Hybrid Warfare |
| Primary Objective | Physical destruction of enemy forces and infrastructure. | Information dominance, network disruption, and decision superiority. |
| Strategic Asset | Manpower, artillery, geographic territory. | Data, cloud infrastructure, computational power (GPUs). |
| Decision Cycle | Linear, human-driven sequential OODA loop. | AI-enabled Super-OODA loop; simultaneous Matrix Operations. |
| Kill Chain Execution | Minutes to hours; heavily reliant on human communication networks. | Milliseconds; automated machine-to-machine targeting and execution. |
| Key Weapons | Tanks, missiles, infantry, naval destroyers. | Cyberattacks, drone swarms, algorithmic targeting, electronic warfare. |
| Corporate Role | Traditional defense contractors (heavy hardware manufacturing). | Big Tech and startups heavily integrated into operational command. |
| Reversibility of Effects | Irreversible physical destruction and casualties. | Often reversible (e.g., recovering from a cyberattack or DDoS attack). |
Conclusion
Data-driven warfare is not a distant, futuristic concept reserved for science fiction—it is the undeniable reality of the contemporary battlespace. The integration of AI into military operations offers unprecedented speed, lethal precision, and total situational awareness.
It effectively compresses the traditional fog of war into manageable, highly actionable insights. Yet, as nations frantically construct their smart combat ecosystems, they must navigate the treacherous waters of technological dependency, ethical accountability, and data sovereignty.
The ultimate victor in tomorrow’s conflicts will not simply be the nation that wields the sharpest physical sword. It will be the nation that controls the most secure, integrated, and fiercely intelligent data fabric.
The transition to data-driven warfare represents a fundamental, irreversible shift in the history of human conflict. The integration of artificial intelligence, autonomous drone systems, and tactical edge computing into military operations offers unparalleled speed, lethal precision, and total situational awareness. It effectively compresses the chaotic fog of war into manageable, highly actionable data streams.
Yet, as nations frantically construct their smart combat ecosystems and predictive defense grids, they must carefully navigate incredibly treacherous waters. The risks of technological dependency on private corporations, the erosion of ethical accountability in targeting, and the urgent need for absolute data sovereignty cannot be ignored. The ultimate victor in tomorrow’s geopolitical conflicts will not simply be the nation that wields the sharpest physical weapon. It will be the nation that masters, secures, and continuously innovates its intelligent data fabric.
FAQ SECTION
Q1: What exactly is Data-Driven Warfare?
Data-driven warfare is a modern military strategy where information—gathered from satellites, drones, and ground sensors—is continuously analyzed using artificial intelligence. This strategy shifts the focus from purely physical combat to achieving “decision dominance.” By processing battlefield data significantly faster than the enemy, militaries enable real-time targeting and rapid command execution.
Q2: How does Artificial Intelligence enhance the traditional OODA loop?
The traditional OODA loop (Observe, Orient, Decide, Act) relies entirely on human sequential thinking. AI enhances this by creating highly adaptive “Super-OODA loops.” Algorithms can process thousands of data points instantly, accurately predict enemy movements, and autonomously recommend actions. This drastically compresses the critical time between identifying a threat and neutralizing it.
Q3: What is the Delta system used in the Ukraine conflict?
The Delta system is an indigenous, highly advanced digital battle management platform used by Ukraine. It securely aggregates data from radar, drones, and human intelligence to create a real-time map of the battlefield. Utilizing AI to identify enemy equipment, Delta allows Ukrainian commanders to coordinate precise strikes efficiently, even functioning completely offline in austere environments.
Q4: What is JADC2 and why is it important to the US Military?
Joint All-Domain Command and Control (JADC2) is a massive US Department of Defense initiative. It is designed to connect sensors and shooters from all military branches into a single unified data network. It aims to eliminate rigid information silos, allowing for seamless data sharing and faster, highly coordinated decision-making across all domains of warfare.
Q5: What is India’s Project Ekam and why was it created?
Project Ekam is an initiative by the Indian Army to create a fully indigenous, secure artificial intelligence platform. Designed under the Atmanirbhar Bharat vision, it ensures national data sovereignty by actively removing reliance on foreign software. It assists military personnel in analyzing intelligence and managing documents within a highly classified digital environment.
Q6: What are the primary ethical concerns of using AI in warfare?
Major ethical concerns include algorithmic bias, which could easily lead AI systems to misidentify innocent civilians as combatants. It also creates an “accountability black hole.” If an autonomous weapon commits a war crime, it is legally difficult to assign blame. Furthermore, it risks dehumanizing conflict by reducing human lives to mere statistical data points.
Q7: How does tactical edge computing benefit military operations?
Edge computing involves processing data locally on devices like drones or wearable soldier tech, rather than sending it to a distant centralized cloud. In modern warfare, this is absolutely crucial. It severely reduces data latency and allows systems to function properly in environments where communication networks have been jammed or destroyed by the enemy.
Q8: What does the Tallinn Manual 2.0 say about targeting military data?
The Tallinn Manual 2.0, a comprehensive study on international law in cyber operations, suggests that data is intangible. Therefore, it does not legally qualify as a physical “object.” Consequently, deleting or altering civilian or military data might not legally constitute a kinetic “attack,” creating a massive, highly complex gray area in international conflict law.
Q9: Why are tech companies becoming central to modern warfare?
Modern militaries lack the internal infrastructure to process massive datasets quickly. Therefore, they rely heavily on private tech companies for cloud computing, AI analytics, and secure satellite communications. Firms like Palantir and SpaceX are now deeply embedded in the operational command structures of sovereign nations, shifting traditional power dynamics.
Q10: What is Matrix Operations in the context of military AI?
Matrix Operations refers to the future phase of AI warfare that moves beyond sequential, step-by-step decision loops. Because AI does not suffer from human cognitive bottlenecks, it can engage in “Matrix Thinking.” This allows military systems to execute multiple, simultaneous, non-linear combat operations across land, air, and cyberspace instantly.





+ There are no comments
Add yours