The Invisible Backbone of National Security
Every smartphone, radar system, missile guidance unit, or banking server relies on one thing—electronic hardware. It quietly powers modern life. Yet, what if the very chips and components inside these systems were compromised?
This is not science fiction. It is a growing global concern.
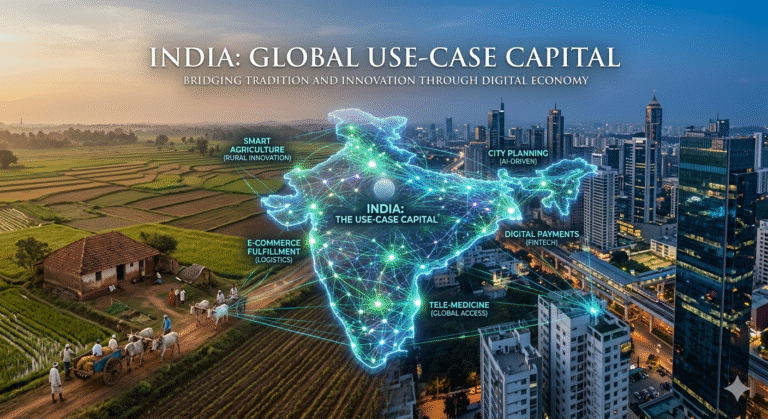
India, one of the fastest-growing digital economies, depends heavily on imported electronic hardware. While software security often dominates headlines, hardware-level vulnerabilities pose deeper and harder-to-detect risks. These risks extend beyond data breaches—they can impact defense systems, financial networks, and critical infrastructure.
Understanding electronic hardware security is no longer optional. It is essential for national sovereignty.
What is Electronic Hardware Security?
Electronic hardware security refers to protecting physical electronic components—such as semiconductors, chips, circuit boards, and embedded systems—from malicious tampering, vulnerabilities, or hidden threats.
Unlike software threats, hardware threats are:
- Harder to detect
- Often irreversible once deployed
- Capable of bypassing software-level protections
Key Components of Hardware Security
- Microprocessors and chips
- Printed Circuit Boards (PCBs)
- Firmware embedded in hardware
- Communication modules
Why This Topic Matters Today
India imports a significant portion of its electronic components, especially semiconductors. This dependency introduces multiple risks:
1. Supply Chain Vulnerability
Foreign manufacturing increases exposure to tampering or espionage.
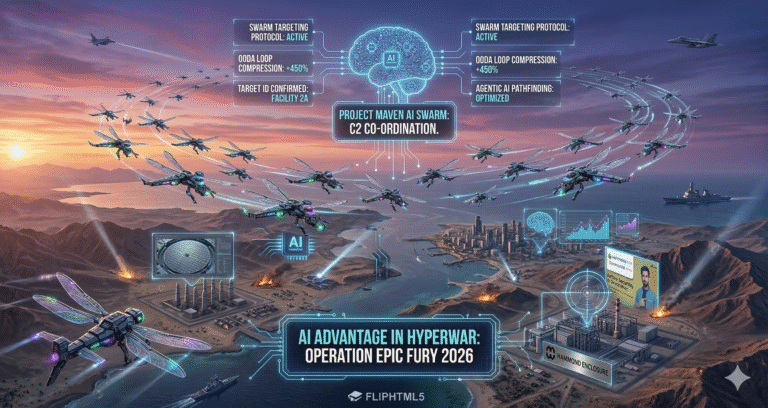
2. National Security Risks
Defense systems relying on imported hardware may carry hidden vulnerabilities.
3. Economic Dependence
Heavy reliance on imports limits technological independence.
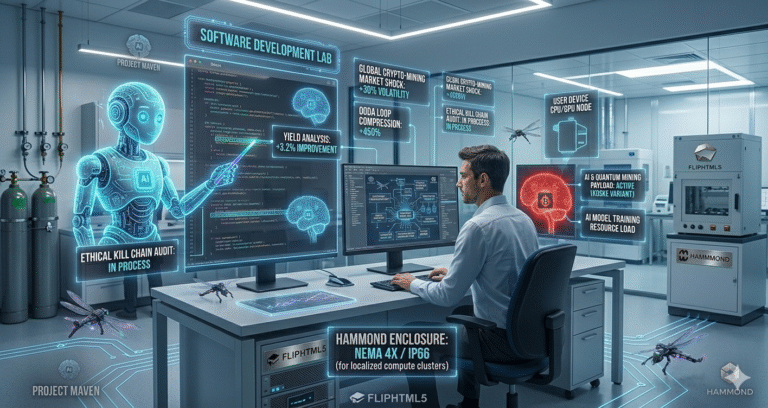
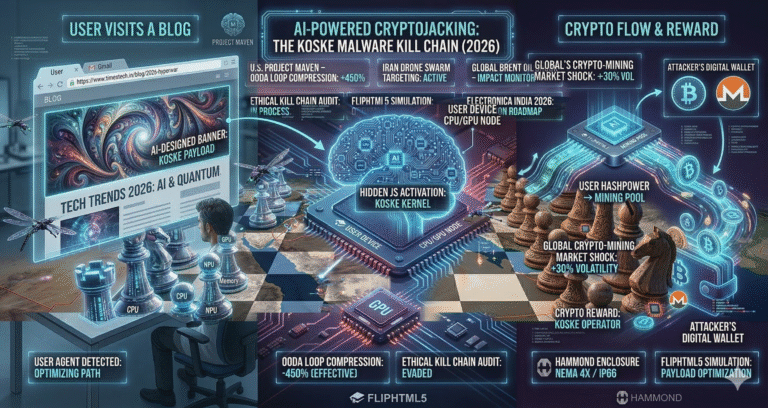
4. Rising Cyber-Physical Threats
Modern attacks combine software exploits with hardware-level manipulation.
Did You Know?
A compromised chip can silently leak sensitive data for years without detection.
Historical Context: How Did We Get Here?
India’s electronics ecosystem has evolved rapidly, but not always strategically.
Phase 1: Import-Led Growth (1990s–2010s)
- Rapid adoption of global electronics
- Minimal focus on domestic manufacturing
Phase 2: Digital Expansion (2010–2020)
- Growth in smartphones, IoT, and digital services
- Increasing reliance on foreign chips
Phase 3: Strategic Awakening (Post-2020)
- Recognition of geopolitical risks
- Push for “Make in India” and semiconductor missions
Understanding the Core Risks
1. Hardware Trojans
Malicious modifications inserted during manufacturing.
Impact:
- Data leakage
- System shutdowns
- Unauthorized access
2. Supply Chain Attacks
Attackers exploit weak points in the manufacturing or distribution chain.
Example:
A component altered during shipping can compromise an entire system.
3. Counterfeit Components
Fake or substandard parts entering the system.
Risks include:
- Reduced reliability
- System failures
- Security loopholes
4. Firmware Exploits
Firmware is often overlooked but critical.
- Hard to update
- Persistent vulnerabilities
- Ideal for long-term attacks
Strategic Framework for Mitigation
To address these risks, a structured approach is essential.
1. Building Trusted Supply Chains
- Identify reliable vendors
- Use certified suppliers
- Implement traceability systems
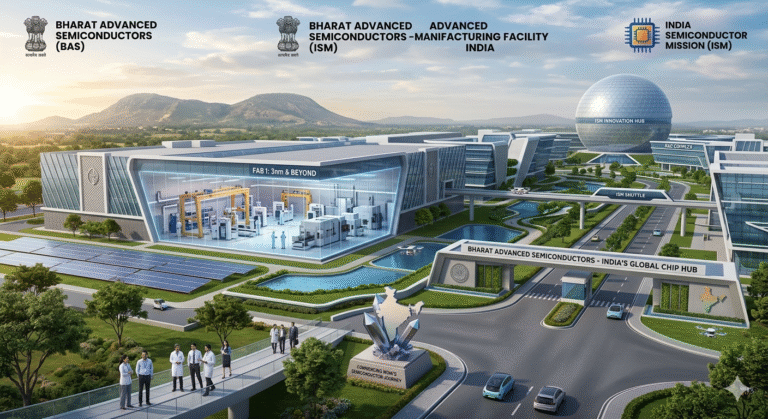
2. Domestic Manufacturing Push
India must invest in:
- Semiconductor fabrication plants
- Chip design capabilities
- Electronics assembly ecosystems
Expert Tip:
Countries that control chip manufacturing control technological power.
3. Hardware Testing & Certification
Implement rigorous testing protocols:
- Security validation
- Integrity checks
- Tamper detection
4. Policy & Regulatory Framework
Government policies should focus on:
- Mandatory security standards
- Import scrutiny
- Vendor certification
5. Public-Private Collaboration
Industry and government must work together:
- Share threat intelligence
- Develop secure technologies
- Invest in R&D
Step-by-Step: How India Can Strengthen Hardware Security
Step 1: Risk Assessment
Identify critical sectors like defense, telecom, and banking.
Step 2: Vendor Verification
Ensure suppliers meet strict security standards.
Step 3: Component Testing
Use advanced labs for verification.
Step 4: Continuous Monitoring
Track hardware performance and anomalies.
Step 5: Incident Response Planning
Prepare for potential breaches.
Real-World Examples
Case Study 1: Global Supply Chain Attacks
Several countries have reported compromised hardware components in critical systems.
Case Study 2: Telecom Infrastructure Risks
Concerns over foreign equipment providers highlight the importance of trusted vendors.
Benefits of Securing Electronic Hardware
| Benefit | Explanation |
|---|---|
| National Security | Protects defense and intelligence systems |
| Economic Growth | Boosts domestic manufacturing |
| Technological Independence | Reduces reliance on imports |
| Data Protection | Prevents unauthorized access |
| Global Competitiveness | Positions India as a trusted tech hub |
Challenges and Risks
1. High Investment Costs
Semiconductor fabs require billions of dollars.
2. Skill Gap
Limited expertise in advanced chip design and fabrication.
3. Global Competition
Countries like the US and China dominate the sector.
4. Rapid Technological Changes
Keeping up with innovation is difficult.
Future Trends in Hardware Security
1. Rise of Trusted Electronics
Governments will prioritize secure hardware ecosystems.
2. AI-Based Threat Detection
AI will help identify hardware anomalies.
3. Indigenous Chip Development
India’s semiconductor mission will gain momentum.
4. Quantum-Safe Hardware
Future systems will resist quantum attacks.
Conclusion: The Road Ahead
India stands at a critical crossroads.
The decisions made today will determine whether the country becomes a global leader in secure electronics or remains dependent on external ecosystems.
Strengthening electronic hardware security is not just a technical necessity—it is a strategic imperative.
The future belongs to nations that control their technology stack from the ground up.
FAQ SECTION
1. What is electronic hardware security?
Electronic hardware security involves protecting physical components like chips, circuit boards, and embedded systems from tampering, vulnerabilities, and malicious attacks. Unlike software, hardware threats are harder to detect and often irreversible. Ensuring hardware integrity is essential for maintaining system reliability and preventing unauthorized access, especially in critical sectors like defense, banking, and telecommunications.
2. Why is hardware security important for India?
India relies heavily on imported electronic components, which increases exposure to supply chain risks. Compromised hardware can impact national security, disrupt critical infrastructure, and lead to data breaches. Strengthening hardware security helps India achieve technological independence and protects sensitive systems from external threats.
3. What are hardware Trojans?
Hardware Trojans are malicious modifications inserted into chips during design or manufacturing. They can remain hidden and activate under specific conditions, causing system failures or data leaks. Detecting them is extremely difficult, making them a serious threat to secure systems.
4. What is a trusted supply chain?
A trusted supply chain ensures that all components come from verified and secure sources. It involves strict vendor verification, traceability, and quality control. This reduces the risk of tampering and ensures the reliability of electronic systems.
5. How can India reduce dependence on imports?
India can invest in semiconductor manufacturing, promote domestic chip design, and support local electronics industries. Government initiatives and public-private partnerships play a crucial role in building a self-reliant ecosystem.
6. What role does the government play?
The government sets policies, enforces security standards, and supports infrastructure development. Initiatives like semiconductor missions and “Make in India” aim to strengthen domestic capabilities and reduce external dependence.
7. What are the biggest challenges in hardware security?
Key challenges include high investment costs, lack of skilled professionals, global competition, and rapidly evolving technology. Overcoming these requires long-term planning and collaboration.
8. Can hardware attacks be detected?
Hardware attacks are difficult to detect because they operate at a low level. Advanced testing methods and continuous monitoring are required, but prevention through secure design is more effective.
9. What industries are most affected?
Critical sectors like defense, telecommunications, banking, healthcare, and energy are most vulnerable. These industries rely heavily on secure and reliable hardware systems.
10. What is the future of hardware security?
The future includes AI-driven detection, indigenous chip manufacturing, and quantum-resistant hardware. Countries will focus on building secure and self-reliant technology ecosystems.



+ There are no comments
Add yours