Introduction: Why Encryption Matters More Than Ever
Every time you send a WhatsApp message, log into your bank account, or make an online payment, something powerful happens behind the scenes.
Your data becomes encrypted.
Without encryption, the internet would be extremely dangerous. Hackers could easily steal passwords, banking information, personal conversations, and confidential business data.
Encryption works like a digital lock that protects information from unauthorized access.
Only the person with the correct key can unlock it.
Today, encryption protects:
- Online banking
- Emails and messaging apps
- Cloud storage
- Government communications
- Military systems
- Cryptocurrency networks
In this detailed guide, we will explore encription techniques, how they work, why they are essential, and how they shape the future of cybersecurity.
Whether you are a beginner, researcher, or professional, this article will help you understand encryption in a simple and practical way.
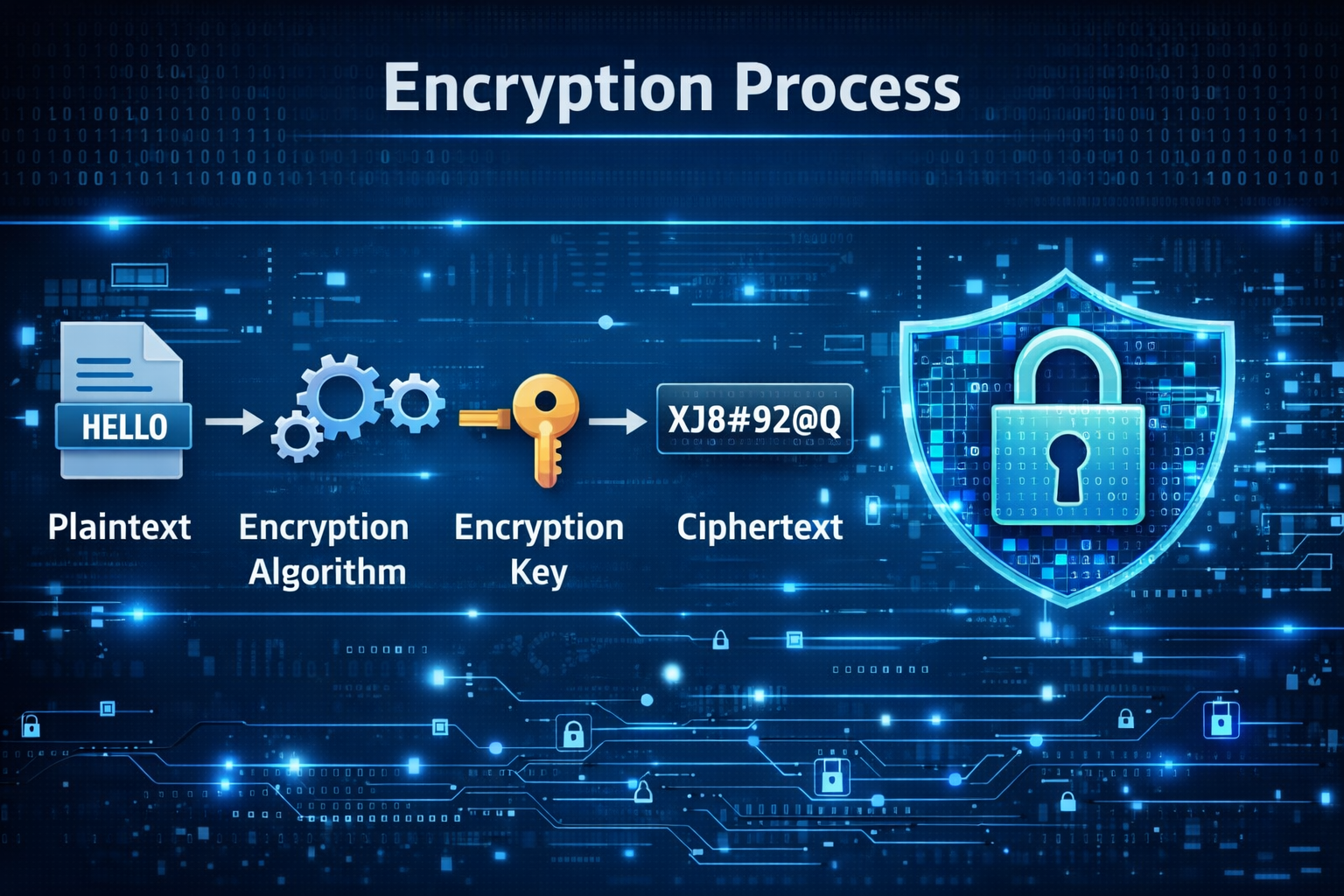
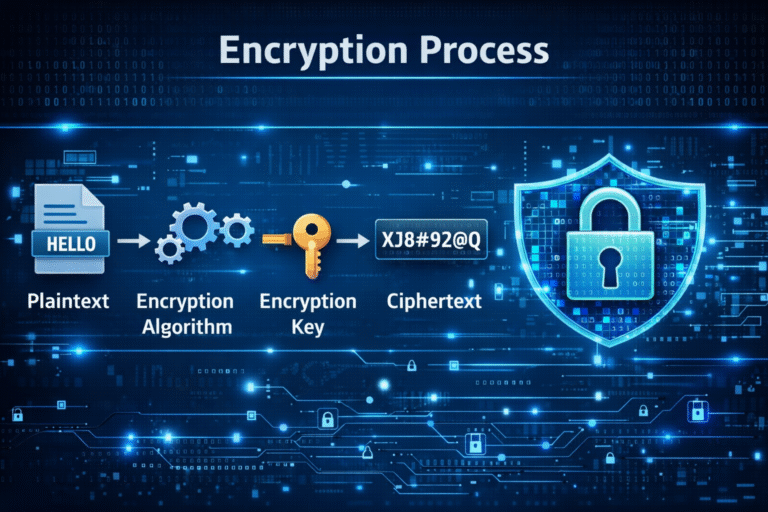
What Is Encryption?
Encryption is the process of converting readable information (plaintext) into unreadable code (ciphertext).
This transformation ensures that only authorized users can access the original information.
Basic Encryption Process
| Step | Description |
|---|---|
| Plaintext | Original readable data |
| Encryption Algorithm | Mathematical process used to encode data |
| Encryption Key | Secret value used for encoding |
| Ciphertext | Encrypted unreadable data |
| Decryption | Converting ciphertext back to plaintext |
Example:
Plain text message:
HELLO
Encrypted version may look like:
XJ8#92@Q
Without the correct key, the message cannot be understood.
Why Encryption Is Important Today
In the digital age, data travels constantly across networks.
Without protection, this data becomes vulnerable to cyber threats.
Major Reasons Encryption Is Critical
1. Protects Personal Data
Encryption keeps sensitive information safe:
- Passwords
- Financial details
- Personal messages
2. Secures Online Transactions
E-commerce websites use encryption to protect payment details.
Look for HTTPS in your browser address bar.
3. Protects Business Information
Companies rely on encryption to secure:
- customer data
- trade secrets
- internal communication
4. National Security
Governments use encryption to secure classified communications.
5. Data Privacy Regulations
Modern regulations like GDPR and data protection laws require strong encryption practices.
For more about protecting digital data, see this guide:
Internal Resource:
Mobile Privacy and Security Tips
https://blog.aquartia.in/mobile-privacy-security
Historical Background of Encryption
Encryption is not new.
It has existed for thousands of years.
Ancient Encryption
Caesar Cipher (50 BC)
Used by Roman leader Julius Caesar.
Each letter in a message was shifted by a fixed number.
Example:
HELLO → KHOOR
This was one of the earliest encryption techniques.
World War Encryption
During World War II, countries used advanced machines like Enigma to encode military messages.
Breaking these codes helped change the outcome of the war.
Modern Cryptography
With the rise of computers and the internet, encryption became more sophisticated.
Modern encryption uses complex mathematics and algorithms that are almost impossible to break.
Organizations like:
National Institute of Standards and Technology
https://www.nist.gov
help define modern encryption standards.
Types of Encryption Techniques
Encryption methods are mainly divided into two major categories.
| Encryption Type | Key Usage | Speed | Security |
|---|---|---|---|
| Symmetric Encryption | One shared key | Fast | Moderate |
| Asymmetric Encryption | Public + private keys | Slower | Very High |
Let’s explore each in detail.
1. Symmetric Encryption
Symmetric encryption uses a single key for both encryption and decryption.
Both the sender and receiver must have the same secret key.
Example Process
- Sender encrypts message using secret key
- Receiver uses same key to decrypt message
Advantages
- Very fast
- Efficient for large data
- Used in databases and storage encryption
Disadvantages
- Key distribution problem
- If the key is stolen, data becomes vulnerable
Common Symmetric Encryption Algorithms
| Algorithm | Description |
|---|---|
| AES | Advanced Encryption Standard |
| DES | Data Encryption Standard |
| 3DES | Triple Data Encryption Standard |
| Blowfish | Fast symmetric encryption algorithm |
AES Encryption
AES is currently the global standard encryption algorithm.
Key sizes:
- 128-bit
- 192-bit
- 256-bit
AES-256 is widely used in:
- banking
- government systems
- secure file storage
More about encryption standards:
https://csrc.nist.gov/projects/cryptographic-standards-and-guidelines
2. Asymmetric Encryption
Asymmetric encryption uses two different keys.
| Key Type | Purpose |
|---|---|
| Public Key | Used to encrypt data |
| Private Key | Used to decrypt data |
Anyone can use the public key, but only the owner has the private key.
Example Process
- Sender encrypts message using receiver’s public key
- Receiver decrypts message using private key
This system solves the key sharing problem.
Popular Asymmetric Algorithms
| Algorithm | Usage |
|---|---|
| RSA | Secure communication |
| ECC | Mobile encryption |
| DSA | Digital signatures |
| Diffie-Hellman | Key exchange |
RSA Encryption
RSA is widely used in:
- email security
- SSL certificates
- digital signatures
Research on modern cryptography is published by institutions like:
Massachusetts Institute of Technology Cryptography Research
https://crypto.mit.edu
End-to-End Encryption (E2EE)
End-to-End Encryption ensures that only sender and receiver can read messages.
Even service providers cannot access the content.
Apps using E2EE:
- Signal
- Telegram (secret chats)
Example Flow
User A → Encrypted Message → Internet → User B
No intermediary can read the data.
Step-by-Step: How Encryption Works Online
Let’s understand encryption in a simple process.
Step 1: Data Creation
User writes message or enters information.
Example:
My password is 12345
Step 2: Encryption Algorithm
System converts the message into ciphertext.
Step 3: Transmission
Encrypted data travels across the internet.
Step 4: Decryption
Receiver decrypts using the appropriate key.
Step 5: Original Message Restored
Plaintext becomes readable again.
Real-World Examples of Encryption
Online Banking
Banks use SSL/TLS encryption to protect transactions.
This ensures:
- card details remain private
- login credentials are protected
Messaging Applications
WhatsApp encrypts billions of messages daily.
Messages cannot be accessed by third parties.
Cloud Storage
Services like Google Drive and Dropbox use encryption to protect stored files.
Cryptocurrency
Blockchain networks rely heavily on encryption techniques to secure transactions.
Benefits of Encryption
Encryption provides many advantages.
| Benefit | Description |
|---|---|
| Data Privacy | Protects personal information |
| Secure Communication | Prevents interception |
| Data Integrity | Ensures data is not altered |
| Authentication | Verifies user identity |
| Compliance | Meets legal requirements |
Did You Know?
Some modern encryption systems would take billions of years to crack using current computers.
This makes them practically unbreakable.
Challenges and Risks of Encryption
Despite its benefits, encryption also has challenges.
1. Key Management
If encryption keys are lost, data becomes permanently inaccessible.
2. Performance Impact
Encryption requires computational resources.
Large systems may experience slower performance.
3. Cybercrime Misuse
Criminal groups sometimes use encryption to hide illegal activities.
4. Quantum Computing Threat
Future quantum computers may break some current encryption algorithms.
Researchers are already working on post-quantum cryptography.
Future of Encryption
Encryption technology continues to evolve rapidly.
Major Future Trends
1. Post-Quantum Cryptography
New encryption algorithms designed to resist quantum attacks.
2. Homomorphic Encryption
Allows computations on encrypted data without decrypting it.
This could revolutionize cloud security.
3. Zero-Knowledge Proofs
Users can prove identity without revealing personal information.
This technology is growing in blockchain systems.
4. AI-Driven Security
Artificial intelligence can detect encryption vulnerabilities and cyber attacks.
Expert Insight
Cybersecurity experts recommend using multi-layer encryption strategies.
This means protecting data at multiple levels:
- network
- device
- storage
- communication
Layered encryption significantly reduces the chances of data breaches.
For deeper cybersecurity concepts, you may explore:
Internal Resource:
Understanding Digital Security and Cyber Protection
https://blog.aquartia.in/digital-security-guide
Practical Tips to Use Encryption Safely
Here are simple practices anyone can follow.
Use Encrypted Messaging Apps
Choose apps with end-to-end encryption.
Enable HTTPS Websites
Always check for HTTPS lock icon in the browser.
Use Strong Password Managers
Password managers encrypt stored passwords.
Enable Device Encryption
Most smartphones allow full-disk encryption.
Use VPN for Public WiFi
VPN encrypts your internet traffic.
Quick Comparison Table of Encryption Types
| Feature | Symmetric Encryption | Asymmetric Encryption |
|---|---|---|
| Number of Keys | 1 | 2 |
| Speed | Fast | Slower |
| Security | Moderate | High |
| Common Use | Data storage | Secure communication |
| Examples | AES, DES | RSA, ECC |
Visual Explanation Suggestions
Suggested diagrams for blog images:
- Encryption Flow Diagram
- Plaintext → Algorithm → Ciphertext → Decryption
- Symmetric vs Asymmetric Encryption Illustration
- End-to-End Encryption Communication Flow
- Internet Data Security Layers
These visuals help readers understand encryption more easily.
Summary
Encryption is one of the most important technologies protecting modern digital communication.
From online banking to messaging apps, encryption keeps information secure from unauthorized access.
Understanding encryption techniques helps individuals and organizations protect their data effectively.
As cyber threats continue to grow, encryption will remain a critical pillar of digital security.
FAQ Section
1. What is encryption in simple terms?
Encryption is the process of converting readable information into coded data so that unauthorized users cannot access it. The information becomes unreadable unless someone has the correct decryption key. Encryption is widely used in internet communication, banking transactions, messaging apps, and cloud storage. It ensures that even if hackers intercept the data, they cannot understand it. Modern encryption algorithms use complex mathematics that makes breaking the code extremely difficult. This is why encryption is one of the most important tools in cybersecurity.
2. What are the main types of encryption?
There are two primary types of encryption: symmetric encryption and asymmetric encryption. Symmetric encryption uses a single key for both encrypting and decrypting the data. It is faster and commonly used for large data storage. Asymmetric encryption uses two keys—a public key and a private key. The public key encrypts the data, while the private key decrypts it. This method is more secure for communication over the internet and is used in technologies such as SSL certificates and secure email systems.
3. Why is encryption important for cybersecurity?
Encryption protects sensitive data from unauthorized access. Without encryption, hackers could easily read passwords, financial information, and personal messages. Encryption ensures that even if data is intercepted during transmission, it remains unreadable. Businesses also rely on encryption to protect intellectual property and confidential information. Governments use encryption to secure classified communication. In short, encryption acts as a protective shield for digital data and is a core component of modern cybersecurity systems.
4. What is end-to-end encryption?
End-to-end encryption (E2EE) ensures that only the sender and receiver can read the message being sent. The message is encrypted on the sender’s device and decrypted only on the receiver’s device. No intermediate server or service provider can access the content. Messaging apps like WhatsApp and Signal use this technology. E2EE protects conversations from hackers, internet providers, and even the platform itself. This makes it one of the most secure communication methods available today.
5. What is an encryption key?
An encryption key is a unique string of characters used by encryption algorithms to convert plaintext into ciphertext and vice versa. It acts like a password that locks and unlocks data. In symmetric encryption, the same key is used for encryption and decryption. In asymmetric encryption, two keys are used: a public key and a private key. The strength of encryption largely depends on the length and complexity of the key used.
6. Is encrypted data impossible to hack?
No encryption system is completely impossible to break, but strong encryption algorithms are extremely difficult to crack. Modern encryption like AES-256 would require an enormous amount of computing power to break using traditional methods. In many cases, it would take billions of years with current technology. However, poor key management, weak passwords, or software vulnerabilities can still expose encrypted data. This is why encryption must be combined with other cybersecurity practices.
7. What is the difference between cryptography and encryption?
Cryptography is the broader field of study that deals with securing communication and protecting information. Encryption is one technique within cryptography. Cryptography includes other processes such as hashing, digital signatures, authentication protocols, and secure key exchange methods. Encryption specifically focuses on converting readable data into encoded data to prevent unauthorized access. In simple terms, encryption is a tool used within the larger discipline of cryptography.
8. How is encryption used in everyday life?
Encryption is used in many everyday technologies. When you log into a website using HTTPS, encryption protects your login details. Messaging apps encrypt conversations to maintain privacy. Online banking uses encryption to secure financial transactions. Cloud services encrypt stored files to protect user data. Even smartphones use encryption to safeguard personal information if the device is stolen. Most internet users interact with encryption multiple times every day without realizing it.
9. Can encryption protect data completely?
Encryption significantly improves data security but should not be the only defense. Effective cybersecurity requires multiple layers of protection including firewalls, secure passwords, multi-factor authentication, and regular security updates. Encryption protects the data itself, but attackers may still target devices or networks. Therefore, organizations combine encryption with other security technologies to create a comprehensive protection strategy.
Key Takeaways
📦 Important Points
- Encryption converts readable data into secure coded information
- Two main types: Symmetric and Asymmetric encryption
- Encryption protects online banking, messaging, and digital communication
- Modern algorithms like AES and RSA provide strong security
- End-to-End Encryption ensures only sender and receiver can read messages
- Future encryption will focus on quantum-resistant algorithms
Conclusion
Encryption has become one of the most essential technologies of the digital era.
Without encryption, modern systems like:
- online banking
- secure messaging
- cloud computing
- digital payments
would not be possible.
As cyber threats continue to evolve, encryption techniques will also become more advanced. Technologies such as post-quantum cryptography, AI security systems, and advanced encryption algorithms will define the future of digital privacy.
For individuals, businesses, and governments, understanding encryption is no longer optional—it is a fundamental part of digital security awareness.
The more we understand encryption, the better we can protect our information in an increasingly connected world.





+ There are no comments
Add yours